

- ����
- 53473
- ���շ���
- ����¼
- 2025-05-08
|
������ֱ������PDF�ĵ�������XX���ֻ�ȡLua�ű�����.zip . ==========================================================����������xx���ֵ�lua�ű����� 1. ��Ѱ����/Library/MobileSubstrate/DynamicLibraries���濴�� XXScreenShot.dylib XXScreenShot.plist Plist�������� <?xml version="1.0" encoding="UTF-8"?><!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd"><plist version="1.0"><dict> <key>Filter</key> <dict> <key>Bundles</key> <array> <string>com.apple.backboardd</string> </array> </dict></dict></plist> ������������hook��backboardd���� 2. ��̬����IDA ���� XXScreenShot.dylib --- �ҵ�loadLuaData���������������� tea�㷨 [attachment=207336] ������һ�£�X23�Ĵ���ָ����������� 3. ��̬���� �ֻ������У�[attachment=207337] Mac�����У�[attachment=207338] 4���¶� [attachment=207339] ��ʱ��Ŀ������ϵ�������š����ýű����� [attachment=207340] 5����������[attachment=207341] ����ǰ����IDA������x23�Ĵ���������������ݣ���ô����ֱ����0x103d12cdc�¶ϵ㣬��ʱx23�Ѿ��õ������ݣ��ºöϵ�������У�����ͼ��˳���ж� [attachment=207342] 6���������[attachment=207343] ��ʱlua�ű��Ѿ����������ˣ����� 7����дtweak���ǿ���д��tweak��ץȡ�ű�����:/* ��ȡxx����lua�ű� By Ʈ��/P.Y.G 2015-04-29 http://www.chinapyg.com*/#import <substrate.h>#import <pthread.h>// ԭʼ����signed int (*orig_XxteaDecrypt)(const char *inBuf, size_t bufLen, const char *key, size_t a4, char *outBuf, int a6);signed int myXxteaDecrypt(const char *inBuf, size_t bufLen, const char *key, size_t a4, char *outBuf, int a6){ signed int ret = orig_XxteaDecrypt(inBuf, bufLen, key, a4, outBuf, a6); NSString *str = [NSString stringWithCString:outBuf encoding:NSUTF8StringEncoding]; //NSLog(@"[++++]%s", outBuf); NSLog(@"[++++]%@", str); return ret;}void *threadFun(void*){ while (true) { void *lpFun = ((void*)MSFindSymbol(NULL, "__Z12XxteaDecryptPKciS0_iPci")); if (lpFun) { NSLog(@"[++++]lpFun = %p", lpFun); MSHookFunction(lpFun, (void*)myXxteaDecrypt, (void**)&orig_XxteaDecrypt); NSLog(@"[++++]orig_XxteaDecrypt = %p", orig_XxteaDecrypt); break; } } return NULL;}static __attribute__((constructor)) void piaoyun(){ // ���߳������ң�����xx��dylib����ض��Ҳ������� pthread_t th; int err = pthread_create(&th, NULL, threadFun, NULL); if (err != 0) printf("[++++]pthread_create error: %s\n", strerror(err)); NSLog(@"[++++]inject success!!!!");}8��Tweak��ʾ 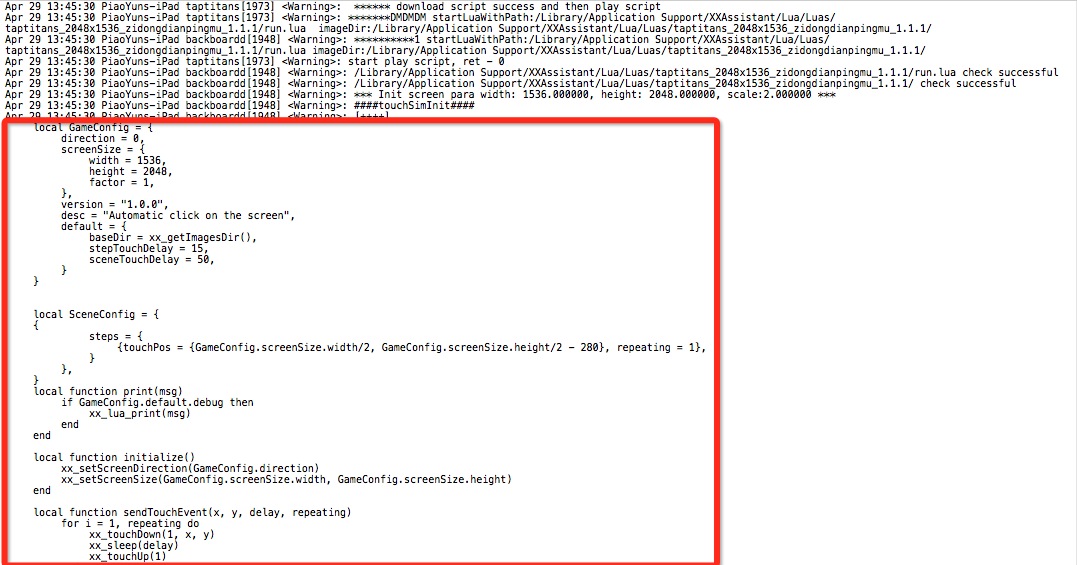 �����Ȼ��Ҳ�����Լ�д������̬����lua�ű����Ҳ�̫ϲ�����ڣ���ֱ��tweak�ˡ��� �����Ȼ��Ҳ�����Լ�д������̬����lua�ű����Ҳ�̫ϲ�����ڣ���ֱ��tweak�ˡ��� [ ������pony8000��2015-04-29 22:01���±༭ ]
|